Parameter
Parameter meaning and representation
F
A collection of files that are outsourced represents a collection of n data files .
.
W
A collection of different keywords that are extracted from the document collection F, representing a collection of p words .
.
I
Index for the establishment of a fuzzy keyword search for privacy preserving.
Tw
After user input search keywords w, the search request is generated by the one-way function, that is Trapdoor.
FIDwi
The file set F contains an ID collection of documents of keywords wi or near wi-syllable word or synonym.
f(key,・),g(key,・)
Pseudo random function (PRF), defined as {0, 1}* × key→ (0, 1).
Enc(key,・)
Dec(key,・)
Symmetric key encryption/decryption function based on semantic security.
ED(w1, w2)
A description method of string similarity. For two words w1 and w2 in the two to achieve the increase of the minimum number of the required to convert, modify or delete the operation of the characters. For a given word w and integer d, with Sw,d representing similar thereto word w’, to meet the .
.
SPw,d
The fuzzy Pinyin of keywords w corresponding to the keyword set. For the given Chinese keywords w and integer d, the Pinyin PYw corresponds to the fuzzy tone set , to meet with the edit distance of keywords w’s Pinyin that is less than d for all similar Pinyin keywords set expressed as
, to meet with the edit distance of keywords w’s Pinyin that is less than d for all similar Pinyin keywords set expressed as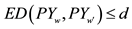 . For any
. For any , the pinyin of
, the pinyin of  is represented as
is represented as .
.
SYw
A set of keywords synonymous with keywords w. different keywords set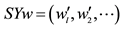 . Describing the same thing in a language are converted into another language,
. Describing the same thing in a language are converted into another language,  generally corresponding to the same keywords we, which is called set
generally corresponding to the same keywords we, which is called set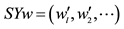 , as a synonym set for keywords w, among them the
, as a synonym set for keywords w, among them the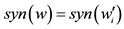 , syn() is synonymous conversion function. This paper uses Chinese and English to achieve the conversion.
, syn() is synonymous conversion function. This paper uses Chinese and English to achieve the conversion.
Fuzzy keyword search
A collection  consisted of n encrypted data files and different predefined keywords set
consisted of n encrypted data files and different predefined keywords set  are given, search keywords w and d input and after the implementation of the synonymous keyword search it will return to the ID file set {FIDwi,}, in which
are given, search keywords w and d input and after the implementation of the synonymous keyword search it will return to the ID file set {FIDwi,}, in which ,
,  or
or .
.
History
The interaction between the user and the cloud server, which is composed of F and a group of keywords, is expressed as .
.
View
According to the secret key K, historical records Hq given, cloud servers can only see encrypted history that is the view of Vk (Hq). It includes index I of document collection f, query keywords trapdoor . Among them
. Among them  and
and .
. , encryption file set C , is expressed as
, encryption file set C , is expressed as .
.